Is Plone Really More Secure Than Drupal and Joomla?
Security is a touchy subject in the Web CMS world in general and very touchy in particular among open source WCXM projects, since open source platforms are frequently accused (often unfairly) of being inherently insecure by dint of their more open development models.
So it's been interesting to watch some Plone adherents contrast their platform's security profile to that of some major competitors. Plone (and its underlying Zope platform) is a kind of elder statesman in the open source WCXM world. But in terms of energy and hype, Plone has gotten superseded in recent years by faster-moving and significantly larger, PHP-based projects like Joomla and Drupal.
Some Impressive Charts
Plone adherents like to point to the National Vulnerabilities Database maintained by the US Department of Homeland Security with the National Institute of Standards and Technology (NIST), to demonstrate that their platform is more secure. Some Plone folks make impressive-looking charts showing how comparatively few vulnerabilities show up for Plone.
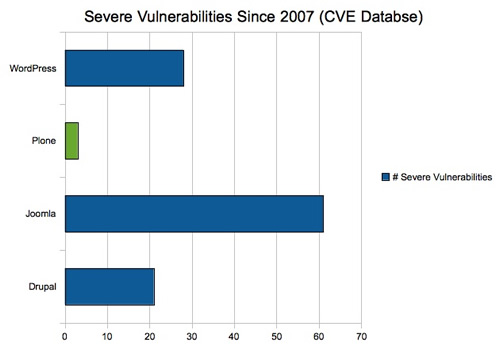
Source: govfresh.com/2011/03/gov-2-0-guide-to-plone/
Source: plonemetrics.blogspot.com/2012/10/last-year-sept-2011-i-responded-to.html
I've seen such charts end up in Plone sales pitches. To be fair, Plone project godfather Alex Limi has made more nuanced comparisons, but the point remains the same: according to NIST, Plone has a better track record.
Does It Really Matter?
Now, it's possible that Python is more secure than PHP, and the Plone/Zope stack may prove more secure than the Joomla/MySQL and Drupal/MySQL stacks. But if so, I'm not sure it matters much.
In the end security is a process you undertake, much more so than an attribute of the technology itself (Limi actually agrees). By extension this means that with enough expertise and ongoing attention, you can maintain a well locked-down Joomla instance.
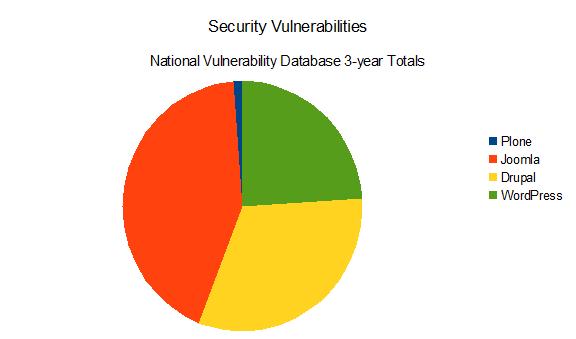
Part of the the issue with Joomla and Drupal is that they are perceived as target-rich environments for bad guys, and therefore get targeted more often. So, if you are running Joomla, you'll have to pay more attention on an ongoing basis than if you're running Plone.
Victims of Success?
To some extent, that's the cost of being more in the mainstream. Let's consider a third chart.
If you were going to target a platform, which would you chose? Perhaps obscurity can indeed sometimes bring more security.
That's why, in our Web Content & Experience Management vendor evaluations, one of the ratings criteria we use is "Threat Prevalence." This reflects how frequently and heavily a platform gets targeted, as well as how successfully. By the way, some commercial platforms don't score well, either.
Finally, it's important to recognize that many security threats stem from internal actors rather than external hackers. That's actually good news; you can usually control your internal environment much more easily than your external website.
Still, the debate rages. What do you think?








